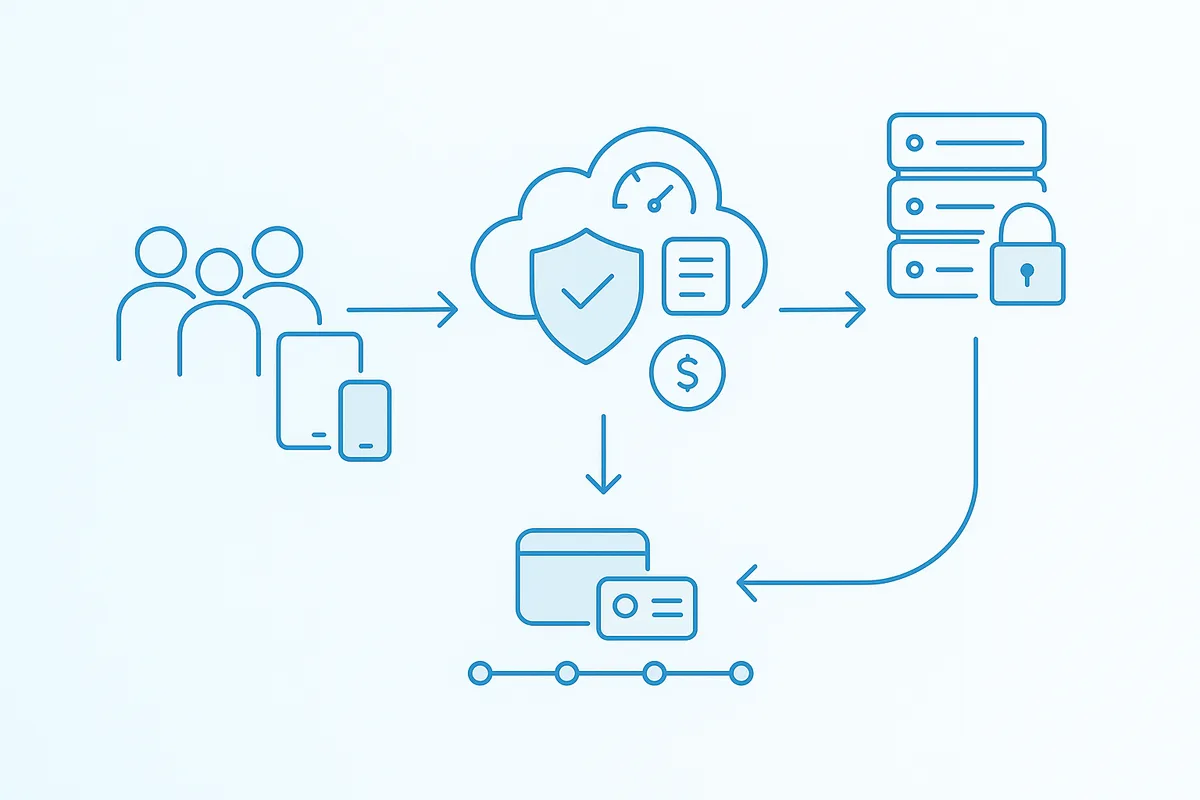
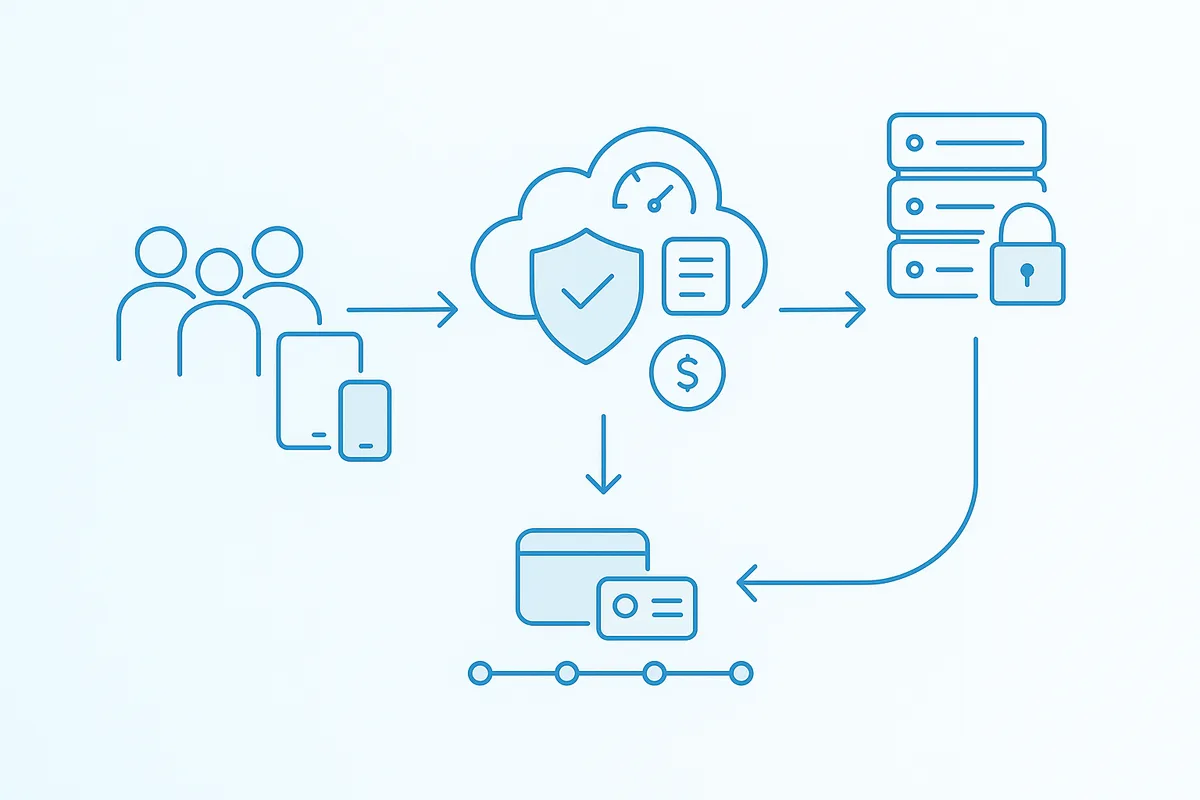
1. Authenticate & Validate
The gateway authenticates the request and resolves the tenant and subject context. Input is validated against policy rules, including request intent, limits, and authorization scope.
Control API usage with ledger-based metering, flexible authentication, and reliable, idempotent billing.
 API Credit Enforcement
API Credit EnforcementEvery usage action - including credit grants, debits, refunds, and adjustments - is recorded as a persistent ledger event. These events are processed with idempotency controls, ensuring that retries or duplicate requests never result in incorrect charges.
 Authentication Compatibility
Authentication CompatibilityWhether you're building new integrations or connecting to legacy systems, the gateway supports multiple authentication methods - all enforced with consistent policy, validation, and auditability.
For most use cases, LicenseSeal uses a combination of:
Additional methods can be enabled where compatibility or security requirements demand it.
Simple and widely supported authentication for server-to-server communication. Includes support for secure storage, rotation, and scoped access.
Short-lived, signed tokens issued by Authority for secure, native integrations. Ensures strong identity verification with minimal exposure risk.
Integrate with your existing identity provider using hosted JWKS. Keys are automatically refreshed, allowing seamless trust with external systems.
Request-level signing for environments requiring deterministic validation. Useful for internal or constrained integrations where token-based auth is not ideal.
Certificate-based authentication for high-security deployments. Provides strong mutual identity verification at the network level.
HTTPS-only key retrieval to protect trust material. Controlled caching and key rotation for consistency and performance. Non-leaking authentication errors to prevent exposure of sensitive details.
 Debit Flow
Debit FlowThis ensures that API usage is validated, charged accurately, and recorded in a way that is safe under retries and concurrency.

The gateway authenticates the request and resolves the tenant and subject context. Input is validated against policy rules, including request intent, limits, and authorization scope.

The system checks available credits and applies policy rules such as allow-negative behavior or usage constraints. Only valid and permitted requests proceed to the debit stage.

The usage debit and corresponding ledger event are written atomically. This guarantees that even under retries or concurrent requests, credits cannot be double-counted or overspent.

The response includes stable event IDs and correlation identifiers, enabling precise tracking for support, reporting, and reconciliation.
 Reporting & Retention
Reporting & RetentionEvery usage event is recorded in a detailed ledger for long-term traceability, while summarized views are generated for day-to-day operations like billing and reporting.

